Download the ArmeSFo Root Certification Authority
Armenian e-Science Foundation (http://www.escience.am/) is an Armenian non-profit institution aimed at the introduction and dissemination of e-Science technologies in Armenian scientific, educational and other organizations. One of the main objectives of ArmeSFo is the deployment of the Grid infrastuctures in Armenia. ArmeSFo CA is an Armenian Certification Authority maintained by ArmeSFo as a courtesy service to the e-Science activities in Armenia.
This is a draft document structured according to the memo “Internet X.509 Public Key Infrastructure Certificate Policy and Certification Practice Framework” [RFC 2527]. This document describes the set of rules and operational practices used by the ArmeSFo CA.
The process of establishing that individuals, organizations, or things are who or what they claim to be. In the context of a PKI, authentication can be the process of establishing that an individual or organization applying for or seeking access to something under a certain name is, in fact, the proper individual or organization. This process corresponds to the second process involved with identification as shown in the definition of the “identification” below. Authentication can also refer to a security service that provides assurances that individuals, organizations, or things are who or what they claim to be or that a message or other data originated from a specific individual, organization, or device. Thus, it is said that a digital signature of a message authenticates the message’s sender.
-
The ArmeSFo CA only guarantees to control the identity of the subjects requesting a certificate according to the practices described in this document;
-
The ArmeSFo CA is run on a best effort only basis and does not give any guarantees about the service security or suitability;
-
The ArmeSFo CA does not warrant its procedures and it will take no responsibility for problems arising from its operation or for the use made of certificates it issues;
- The ArmeSFo CA denies any financial or any other kind of responsibilities for damages or impairments resulting from its operation.
Types of information to be kept confidential
The only confidential information kept by ArmeSFo CA is a photocopy of the subscriber’s organization identity card or organization official document proving the relation of the subscriber with the organization.
Types of information not considered confidential
The ArmeSFo CA collects the following information that is not considered confidential:
- The subscriber’s full name;
- A photocopy of the subscriber passport;
- The subscriber’s e-mail address;
- The subscriber’s organization address;
- The subscriber’s certificate request file;
- The subscriber’s public key file.
The information included in issued certificates and CRLs is not considered confidential. Under no circumstances will the ArmeSFo CA have access to the private keys of any subscriber to whom it issues a certificate.
Disclosure of certificate revocation/suspension information
The ArmeSFo CA will notify and inform the following entities:
- The subject of the personal certificate;
- The requestor of the server or service certificate.
Release to law enforcement officials
The information collected by the ArmeSFo CA will be made available to the law enforcement officials upon their request.
Release as part of civil discovery
The information collected by the ArmeSFo CA will be subject to the law of the Republic of Armenia.
Disclosure upon owner’s request
The information collected by the ArmeSFo CA will be subject to the law of the Republic of Armenia.
Other information release circumstances
The information collected by the ArmeSFo CA will be subject to the law of the Republic of Armenia.

Initial Registration
- The names specified in the common name, in the organization name and in the organizational unit name must be meaningful. The names must be related with the subject organization and with the subject real name.
- For persons, the CN must be obtainable from the legal person name as presented in an official governmental identity document such as a passport or identity card.
- For servers and grid hosts, the CN must be formed from the FQDN.
- For a service, the CN must be related to the type of service and the FQDN of the server where the service is running.
Instructions for requesting personal, server/host or service certificates from Armenian e-Science Foundation Certification Authority (ArmeSFo CA)
1 Introduction
This document describes the steps, which have to be done in order to request personal, server, host or service certificates from ArmeSFo CA. It is based on the ArmeSFo CA Certificate Policy and Certification Practice Statement (CP/CPS) document available at http://www.escience.am.
Before starting the process of application for ArmeSFo CA certificate, you have to read the ArmeSFo CA CP/CPS, understand its policy, requirements to the certificate requestors, obligations of the subscribers of the ArmeSFo CA certificates and agree to follow the CP/CPS and all operational procedures derived from this document.
2 Who can request ArmeSFo CA certificate?
ArmeSFo CA issues certificates to physical persons, servers, hosts and services. The entities that are eligible for certification by the ArmeSFo CA are all those entities related to the organisations formally based in and/or having offices inside the Republic of Armenia, that are involved in the research or deployment of multi-domain distributed computing infrastructures, intended for cross-organisational sharing of resources.
3 Choose the subject distinguished name (DN) of the certificate
Requesters of the certificate have to determine the subject DN of the certificate before they apply for a certificate. You can write down the subject DN on the paper to use it when generating certificate request.
|
The use of printable characters in the DN: The following characters are allowed: Upper and lower case letters: ‘a’-‘z’, ‘A’-‘Z’, Numbers: ‘0’-‘9’, Characters: ‘(‘, ‘)’, ‘+’, ‘,’, ‘-‘, ‘.’, ‘:’, ‘?’, ‘ ‘,‘/’, that is, left and right parentheses, plus, comma, minus/hyphen, dot (period), colon, question mark, space and forward slash. Note: In order the forward slash to be interpreted by openssl as a standard visible character it must be prefixed by the backslash (‘’). |
The subject DN must have the following form:
“/C=AM/O=ArmeSFo/O=organisationName/OU=organisationalUnitName/CN=common Name”.
You have to replace organisationName and organisationalUnitName and commonName
with relevant to your organisation and organisational unit names.
The value of the commonName will correspond either to your full name (for personal certificate) or to the server/host name (for server/host certificate), or to the service name (for service certificate)
3.1 organisationName
Use the official acronym of your organisation/institution.
For example, if you are working in the Yerevan Physics Institute, choose
‘O=YerPhI’
If your organisation has no official acronym, choose its full official name. For example, ‘O= Some Institute’
3.2 organisationalUnitName
Put the official acronym or the full name of your division/department/laboratory in the organisation
For example, ‘OU=Experimental Division’
3.3 commonName
The commonName value in CN field differs in the case of personal, server/host and service certificates.
3.3.1 commonName for personal certificates
Put your common name in the form
Please note, that your first and last names must be identical to those in your passport. Do not write CN=Hakob Hakobian if you have Hakob Hakobyan in your passport.
3.3.2 commonName for server/host certificates
The value of commonName for a server/host is its fully-qualified domain name (FQDN). For example, ‘CN=aligrid1.yerphi.am’
3.3.3 commonName for service certificate
The value of commonName for a service is the service name separated by slash from fully-qualified domain name (FQDN) of the server/host where the service runs
For example, ‘CN=ldap/aligrid1.yerphi.am’
4 Generate certificate request (CR)
The instructions given in this section assume that you are using Unix-like OS with OpenSSL software included in. If you are user of the other operating system, refer to https://www.openssl.org/community/binaries.html page.
In the commands presented below ‘$’ represents the shell prompt (it should not be typed!).
If you are planning to have certificate for working in Grid, issue the following commands:
$ mkdir ~/.globus
$ cd ~/.globus
If you are not planning to work in Grid, we advise you to issue the following commands:
$ mkdir ~/.private
$ cd ~/.private
Run the following command to generate your CR:
$ openssl req -sha512 -newkey rsa:2048 -keyout userkey.pem -out userreq.pem - subj
|
Note: This command should be typed as one line and you have to replace
|
Examples of subject DN strings:
for personal certificate: “/C=AM/O=ArmeSFo/O=YerPhI/OU=Experimental
Division/CN=Hakob Hakobyan”
for server/host certificate: “/C=AM/O=ArmeSFo/O=YerPhI/OU=Experimental
Division/CN=aligrid1.yerphi.am”
for service certificate: “/C=AM/O=ArmeSFo/O=YerPhI/OU= Experimental
Division/CN=ldap/aligrid1.yerphi.am”
You will be asked for your private key password – choose one with at least 12 characters long (see ArmeSFo CA CP/CPS, Section 1.1.1, Strong pass-phrase).
As a result, you will get 2048-bit RSA private and public key pair. The private key is stored in the file userkey.pem, while the public key is stored together with the DN in the file userreq.pem.
Change the permissions of your private key file:
$ chmod 400 userkey.pem
5. Verify the subject DN of your CR:
$ openssl req -in userreq.pem -subject -noout
6. Your steps after generation of CR:
6.1 Read the ‘Minimum Security Requirements of ArmeSFo CA’ (http://www.escience.am)
6.2 If you are requesting user certificate, then
6.2.1 Copy the userreq.pem file to the USB flash or CD/DVD, or floppy disk.
6.2.2 Prepare following documents and data: Your passport (or ID card),
Copy of your passport (ID card),
Official document from your organisation proving your relations with the organisation, signed and stamped by an official representative of the organisation. See Appendix for an example of such document.
Your work e-mail address and personal phone number
|
Note: ArmeSFo CA does not accept the e-mail addresses at social mail servers like yahoo.com, gmail.com, mail.ru, list.ru, rambler.ru, etc. The CRs sent from these addresses will be rejected. |
6.2.3 Send message to Registration Authority of ArmeSFo CA in ArmeSFo using the following e-mail address:
The subject of your message should be:
User certificate request from
The body of your message should be:
Dear RA,
I have read the ArmeSFo CA CP/CPS and ‘Minimum Security Requirements of ArmeSFo CA’ to subscribers and agree to follow these documents. I would like to meet with the personnel of ArmeSFo RA in order to present my CR and requested documents.
The RA will appoint a face-to-face authentication meeting with you, where you will present the requested data, documents and CR.
6.3 If you are requesting server/host or service certificates (you can do that only if you have a valid ArmeSFo CA user certificate and you are the system administrator of the server/host), then your steps are as follows:
6.3.1 Using your private key and certificate, you have to generate the user certificate in pkcs#12 format, which is used for signing the message.
Create the pkcs#12-format certificate with the following command:
$ openssl pkcs12 -export -in usercert.pem -inkey userkey.pem -out usercert.p12
You will be asked for two passwords: the password of the private key, which was set when generating the key pair and the password for creating pkcs#12 file (asked twice)
6.3.2 Install a mail agent that handles with the certificates in pkcs#12 format (we recommend the Open Source mail agent Thunderbird available for both Windows and Linux platforms http://www.mozilla.com/en-US/thunderbird/) and import to the agent usercert.p12 and ArmeSFo CA root certificate (from http://escience.am/ca/cacert/cacert.pem).
6.3.3 Send digitally signed message to [email protected]
The subject of your message should be: (Host, Server, Service) certificate request for
The message must contain short description of the purpose of the use of the (host, server, service) certificate.
The message must also contain the statement that you are the administrator of the host/server.
|
Note: The content of certificate request file has to be included in the body of the message. |
7 Certificate delivery to subscribers
The accepted CRs will be sent to ArmeSFo CA for the certificate issuance. As soon as the certificate is issued, it will be sent to you by ArmeSFo CA via digitally signed e-mail.
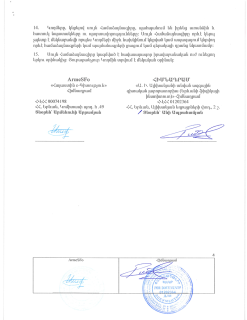
Certificate Revocation Request
The ArmeSFo CA is managed by the CP&IT Division at Alikhanyan National Science Laboratory.
AANL CP&IT Division
2 Alikhanian Brothers Street
0036 Yerevan Armenia
Phone: (+37410) 342088
Email: [email protected]
ArmeSFo CA contact person at AANL
Robert Avetyan
Email: [email protected]